What If Your CMDB Already Knew What's Vulnerable?
Your CMDB knows every server, every application, every dependency. Your vulnerability scanner knows every CVE. Your service desk knows every open ticket.
Three systems. Three databases. Three teams. Zero connection between them.
What if they were one?
The Disconnect Nobody Talks About
Think about how vulnerability management works in most organizations today.
The scanner finds CVEs. It dumps them into a spreadsheet or a dedicated vulnerability platform. A security analyst triages them — maybe. If the CVE is critical enough, someone opens a ticket in the service management tool. That ticket gets assigned to an ops team that has to figure out which servers are affected by going back to the CMDB and searching manually.
Four handoffs. Three tools. And somewhere between step two and step three, context gets lost.
The scanner doesn't know that the affected server runs your payment processing service. The service desk doesn't know that the same vulnerability exists on 14 other machines. The CMDB doesn't know that 80% of those CVEs were already patched last Tuesday.
Everyone has a piece of the puzzle. Nobody has the picture.
What a CMDB Should Actually Know
A CMDB that only tracks hardware specs and IP addresses is a glorified inventory list. It answers "what do we have?" but not "what's at risk?" or "what should we fix first?"
Imagine a CMDB that knows:
- This server runs Apache 2.4.58 — discovered automatically, not entered manually
- Apache 2.4.58 is affected by 23 CVEs — matched against exact version ranges, not just product name
- 15 of those CVEs are already patched — because it also knows which hotfixes are installed
- Of the remaining 8, two have active exploits in the wild — scored by real-world exploitation probability
- This server is part of your payment processing chain — because the CMDB also maps service dependencies
- Patching it requires a change window — because it knows the business impact and who to notify
That's not three systems stitched together with CSV exports. That's a single platform where asset data, vulnerability intelligence, and service context coexist.
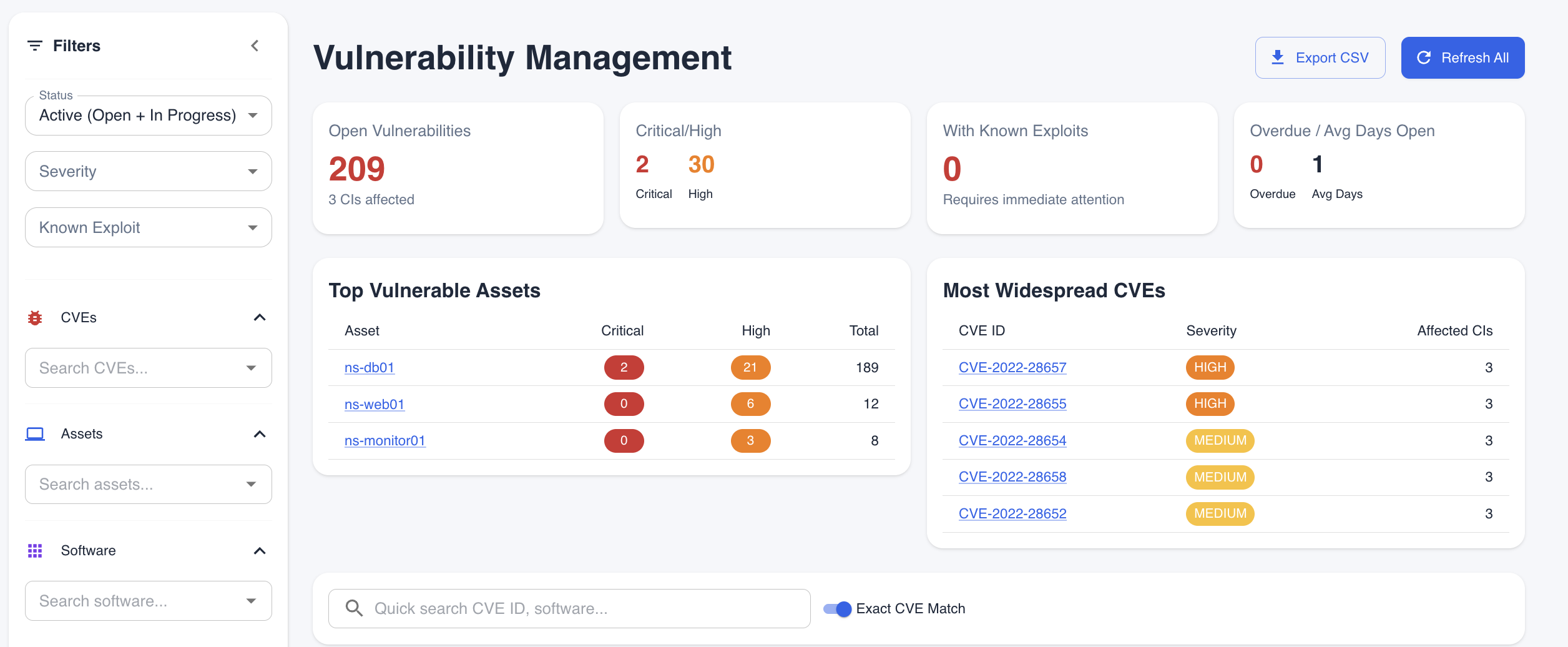 One dashboard. Open vulnerabilities, critical/high breakdown, top vulnerable assets, most widespread CVEs — all tied to your CMDB.
One dashboard. Open vulnerabilities, critical/high breakdown, top vulnerable assets, most widespread CVEs — all tied to your CMDB.
From Inventory to Intelligence
Traditional IT workflows treat these as separate disciplines:
| Discipline | Tool | Team | Output |
|---|---|---|---|
| Asset Management | CMDB | IT Ops | "We have 847 servers" |
| Vulnerability Management | Scanner | Security | "We found 12,000 CVEs" |
| Patch Management | WSUS / SCCM | Infrastructure | "We deployed KB5035434" |
| Service Management | ITSM Tool | Service Desk | "Ticket #4821 assigned" |
Each tool does its job well. But they operate in silos. And the gaps between them are where risk hides.
What if the CMDB was the vulnerability platform? What if discovering a server also meant knowing its CVE exposure? What if the same system that maps your service dependencies also tells you which vulnerabilities sit on critical path?
That's the shift — from inventory to intelligence.
How This Changes Everything
Change Management Gets Smarter
You're planning a server upgrade. Today, the CAB asks: "What's the risk?"
With a vulnerability-aware CMDB, the answer includes: "This server currently has 4 unpatched CVEs with known exploits. The upgrade will resolve 3 of them. The remaining CVE affects a library that isn't in the upgrade scope — here's the separate patch."
The change request doesn't just assess operational risk. It factors in security posture before and after the change.
Incident Response Gets Context
A security alert fires: CVE-2024-21338 is being actively exploited. The question is always the same — "Are we affected?"
When your CMDB tracks vulnerabilities per CI, the answer is immediate: "Yes. 6 servers are affected. 4 are patched. 2 are not — here they are, here's what they run, here's their business impact, and here's who owns them."
No spreadsheet cross-referencing. No waiting for the security team to "investigate and get back to you." The data is already connected.
Compliance Stops Being a Fire Drill
Auditors ask: "Show me your vulnerability remediation process."
Instead of assembling evidence from 3 systems over 2 weeks, you show them a single trail: CVE discovered → matched to CI → assigned to owner → remediated → verified — with timestamps, status history, and business context at every step.
The audit evidence isn't assembled. It's a byproduct of how the system already works.
Version-Aware Matching: Why Accuracy Matters
Most vulnerability tools match on product name alone. You have SQL Server? Here are 400 CVEs that mention SQL Server. Never mind that 350 of them affect versions you don't run.
A CMDB that knows your exact software versions can do something fundamentally different: match CVEs against actual version ranges.
- Apache 2.4.58? Only CVEs where
versionStartIncluding ≤ 2.4.58ANDversionEndExcluding > 2.4.58 - Windows Server 2022 with KB5035434? Exclude every CVE that KB addresses
- SQL Server 2019 CU25? Only CVEs not fixed in that cumulative update
The difference is dramatic. Instead of thousands of "maybe" CVEs, you get dozens of "definitely" CVEs. Your security team works from a list they can actually trust.
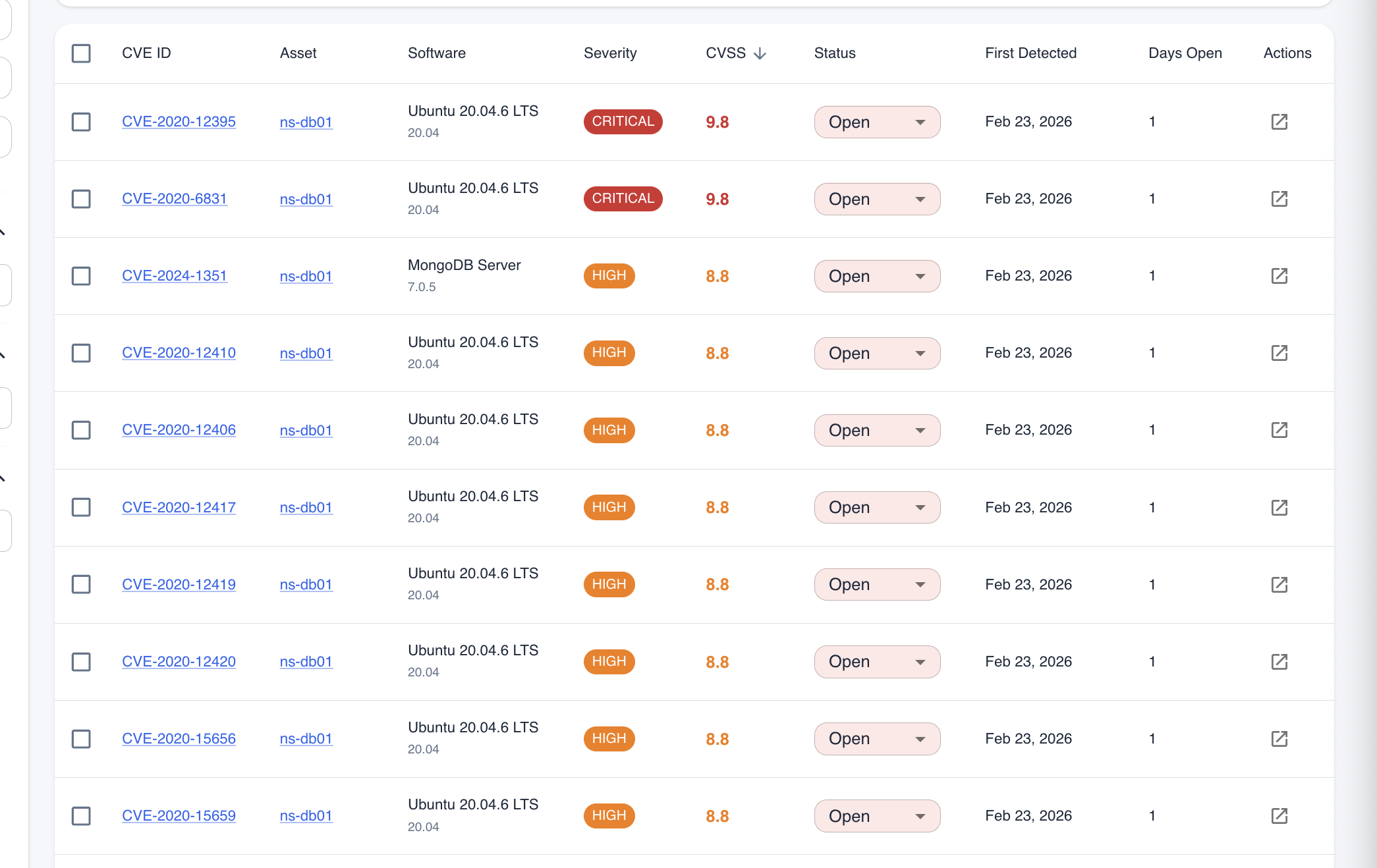 Every CVE tied to an asset, with severity, CVSS score, status, and days open. Sortable, filterable, actionable.
Every CVE tied to an asset, with severity, CVSS score, status, and days open. Sortable, filterable, actionable.
Click into any CVE and you get the full picture — affected asset, software and vendor, CVSS breakdown, description, detection timeline, and a direct link to the NVD entry.
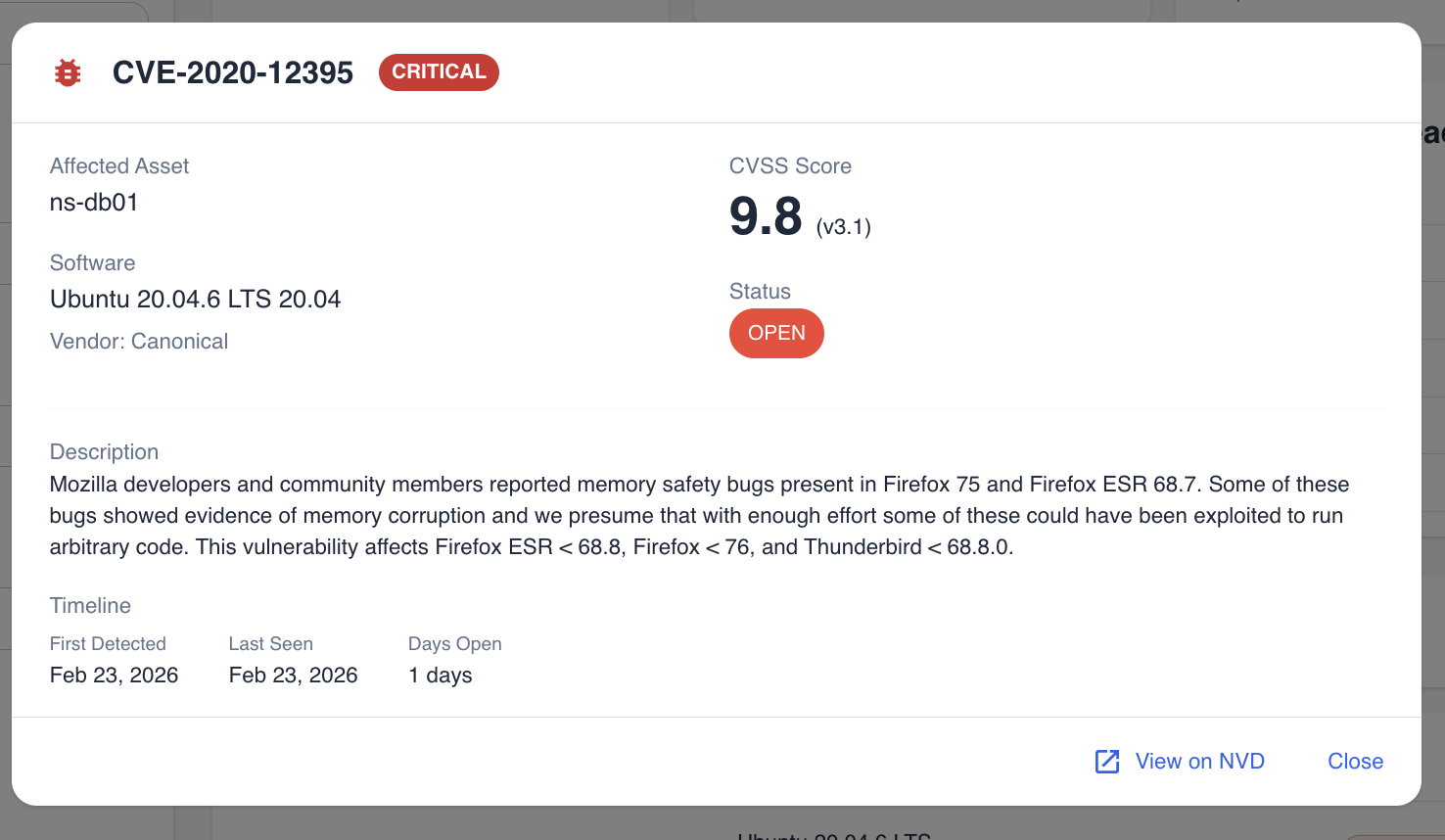 CVE-2020-12395 on ns-db01. CRITICAL, CVSS 9.8. Affected software, status, timeline — everything in one place, linked to the CI.
CVE-2020-12395 on ns-db01. CRITICAL, CVSS 9.8. Affected software, status, timeline — everything in one place, linked to the CI.
And because it's in the CMDB, every CVE is automatically linked to the CI it affects, the services that depend on it, and the team responsible for it.
The Service Management Connection
Here's where it gets interesting.
When vulnerability data lives inside the CMDB — not in a separate security platform — it becomes part of the service management workflow naturally:
Discovery finds a server → Software inventory identifies installed packages → CVE matching finds vulnerabilities → KB correlation excludes patched ones → Service mapping shows business impact → Remediation tracking manages the fix through completion.
One flow. One platform. One record per vulnerability per CI — with full lifecycle tracking from discovery to resolution.
Far fewer integrations to maintain. Far less context lost in translation.
Where This Is Heading: From CVE to Incident to Resolution
Today, Tripl-i handles discovery, version-aware CVE matching, KB correlation, and per-CI vulnerability tracking. But that's only half the story. Here's what becomes possible when vulnerability data lives natively inside your CMDB and service management platform.
Automatic Incident Creation
When a critical CVE is detected on a production server, the system could create an incident automatically — with the CI, affected software, CVSS score, and dependent business services already attached. No manual ticket creation. No copy-pasting CVE details into a service desk form. The incident would be born with full context, because the CMDB already has it.
SLA Tracking by Severity
With vulnerability-driven incidents tied to CMDB data, SLA enforcement becomes natural:
| Severity | Response SLA | Resolution SLA |
|---|---|---|
| Critical (CVSS 9.0+) | 4 hours | 24 hours |
| High (CVSS 7.0-8.9) | 8 hours | 72 hours |
| Medium (CVSS 4.0-6.9) | 24 hours | 7 days |
| Low (CVSS < 4.0) | 48 hours | 30 days |
SLA clocks would start ticking the moment the CVE is matched. If a critical vulnerability on a payment server sits unacknowledged for 3 hours, the right people get escalated — not because someone remembered to follow up, but because the system enforces it.
Auto-Remediation on Upgrade
Here's where the closed loop gets interesting: when the next discovery scan detects that the vulnerable software has been upgraded or the relevant patch has been installed, the vulnerability can be automatically resolved — and the associated incident closed.
The flow becomes self-healing:
- CVE detected → Incident created with SLA
- Ops team patches the server → Next discovery scan runs
- New software version detected → CVE no longer matches → Vulnerability status set to Remediated
- Incident auto-closed with resolution notes: "Resolved — software upgraded from 2.4.58 to 2.4.62, CVE no longer applicable"
No manual ticket closure. No "did we fix that one?" follow-ups. The CMDB verified it, so the incident is resolved.
This is the direction we're building toward — turning vulnerability management from a reactive, ticket-heavy process into a self-healing loop: detect, alert, patch, verify, close — with humans in the loop for decisions, not for paperwork.
What This Looks Like in Practice
| Traditional Approach | Integrated Approach |
|---|---|
| Scanner finds CVE, exports to spreadsheet | CVE automatically matched to CI during discovery |
| Security team manually maps CVEs to servers | Version-aware matching does it at scan time |
| "Are we patched?" requires checking WSUS separately | KB-CVE correlation answers instantly per server |
| "What's the business impact?" requires asking around | Service dependency map shows impact automatically |
| Someone creates a ticket manually for critical CVEs | Incidents can be created automatically with full CI context |
| SLA? What SLA? | Severity-based SLA clocks can start at detection |
| "Did we fix that?" — check 3 systems | Can auto-resolve when next scan confirms the upgrade |
| Remediation tracked in ITSM with no vulnerability context | Per-CI vulnerability lifecycle with full audit trail |
| Compliance evidence assembled manually before audits | Audit trail is a natural byproduct |
The Bigger Picture
The industry has spent years building specialized tools for every discipline — and then building integrations to connect them. CMDB to vulnerability scanner. Scanner to ITSM. ITSM back to CMDB. Each integration is a point of failure, a data sync delay, and a context gap.
The alternative is simpler than it sounds: put the data in one place.
When your CMDB knows what software is installed, what version it is, what CVEs affect that version, which patches are applied, what services depend on that server, and who owns it — you don't need a separate vulnerability platform. You don't need CSV exports and manual triage. You don't need 3 weeks to answer "are we exposed?"
You just look.
Where We're Headed
Vulnerability management shouldn't be a separate discipline with separate tools and separate teams. It should be a dimension of your CMDB — just like location, ownership, or compliance status.
A server isn't just "active" or "in maintenance." It's also "3 unpatched CVEs, 1 with active exploit, remediation in progress, ETA Thursday."
That's not a vulnerability report. That's a CI attribute — visible to everyone who needs it, from the security analyst to the change manager to the service desk agent.
Your CMDB already knows your infrastructure. It should also know what's at risk — and what to do about it.
Tripl-i integrates vulnerability intelligence directly into the CMDB — version-aware CVE matching, Microsoft KB-CVE correlation, and per-CI remediation tracking. No separate vulnerability platform needed. Learn more about vulnerability management or explore KB-CVE mappings.
